目前bfinject的项目源码仅支持Dylib注入的系统为iOS 11.0 - 11.1.2, 但是现在手头有一台最新越狱的iOS 11.3,那么怎样使用bfinject来脱壳呢?
安装bfinject Electra越狱用户: 安装后运行 bash bfinject会报错: [!] Unknown jailbreak. Aborting.
分析Unknown jailbrek报错原因
查看源码: [Bash shell] 纯文本查看 复制代码 #
# Detect LiberiOS vs Electra
#
if [ -f /bootstrap/inject_criticald ]; then
# This is Electra
echo "[+] Electra detected."
cp jtool.liberios /bootstrap/usr/local/bin/
chmod +x /bootstrap/usr/local/bin/jtool.liberios
JTOOL=/bootstrap/usr/local/bin/jtool.liberios
cp bfinject4realz /bootstrap/usr/local/bin/
INJECTOR=/bootstrap/usr/local/bin/bfinject4realz
elif [ -f /jb/usr/local/bin/jtool ]; then
# This is LiberiOS
echo "[+] Liberios detected"
JTOOL=jtool
INJECTOR=`pwd`/bfinject4realz
else
echo "[!] Unknown jailbreak. Aborting."
exit 1
fi
目前最新的Electra越狱后系统里找不到文件路径:/bootstrap/inject_criticald,搜索一下inject_criticald确实存在该文件。 原来如此,bootstrap目录名更改为electra了,
[Bash shell] 纯文本查看 复制代码 tree-flys-iPhone-7:~ root# ls /electra/
amfid_payload.dylib helloworld inject_criticald jailbreakd jailbreakd_client libjailbreak.dylib pspawn_payload.dylib
FIX 1考虑到向低版本iOS兼容性,尽量减少修改源代码 创建软连接 [Bash shell] 纯文本查看 复制代码 ln -s /electra /bootstrap 手动创建代码中的文件夹 [Bash shell] 纯文本查看 复制代码 mkdir /bootstrap/usr
mkdir /bootstrap/usr/local
mkdir /bootstrap/usr/local/bin 完毕后,执行命令 bash bfinject -P AVPlayer.app -L test [Bash shell] 纯文本查看 复制代码 tree-flys-iPhone-7:~/bfinject root# bash bfinject -P AVPlayer.app -L test
[+] Electra detected.
bfinject: md5: command not found
bfinject: md5: command not found
[+] Injecting into '/var/containers/Bundle/Application/B36F534E-DF04-4BBF-987B-EED3E4B3A6AC/AVPlayer.app/AVPlayer'
[+] Getting Team ID from target application...
[+] Thinning dylib into non-fat arm64 image
[+] Signing injectable .dylib with Team ID DR9UPY28XM and platform entitlements...
jtool /bootstrap/usr/local/bin/ signing error. barfing.
分析 md5: command not found原因报错的代码行: [Bash shell] 纯文本查看 复制代码 # Use random filenames to avoid cached binaries causing "Killed: 9" messages.
RAND=`dd if=/dev/random bs=1 count=16 2>/dev/null | md5`
RANDOM_NAME="${INJECTOR%/*}/`dd if=/dev/random bs=1 count=16 2>/dev/null | md5`"
看上去md5文件缺失,这个比较好解决
[Bash shell] 纯文本查看 复制代码 tree-flys-iPhone-7:~/bfinject root# md5
bash: md5: command not found 方法比较多,编译一个md5即可;或者采纳openssl,如openssl md5,或者使用GNU工具命令如md5sum,注意处理下前缀或后缀。 [Bash shell] 纯文本查看 复制代码 tree-flys-iPhone-7:~/bfinject root# echo 'chinapyg.com' | md5sum
a24c26e8ba09235dab371b04e5b58936 -
tree-flys-iPhone-7:~/bfinject root# echo 'chinapyg.com' | md5sum | sed 's/ .*//'
a24c26e8ba09235dab371b04e5b58936
tree-flys-iPhone-7:~/bfinject root# echo 'chinapyg.com' | openssl md5
(stdin)= a24c26e8ba09235dab371b04e5b58936
tree-flys-iPhone-7:~/bfinject root# echo 'chinapyg.com' | openssl md5 | sed 's/.* //'
a24c26e8ba09235dab371b04e5b58936
FIX 2
尝试使用md5sum替代md5,修正下代码: [Bash shell] 纯文本查看 复制代码 #RAND=`dd if=/dev/random bs=1 count=16 2>/dev/null | md5`
RAND=`dd if=/dev/random bs=1 count=16 2>/dev/null | md5sum | sed 's/ .*//'`
#RANDOM_NAME="${INJECTOR%/*}/`dd if=/dev/random bs=1 count=16 2>/dev/null | md5`"
RANDOM_NAME="${INJECTOR%/*}/`dd if=/dev/random bs=1 count=16 2>/dev/null | md5sum | sed 's/ .*//'`"
​
# Debug info
echo "*** RAND = $RAND"
echo "*** RANDOM_NAME = $RANDOM_NAME"
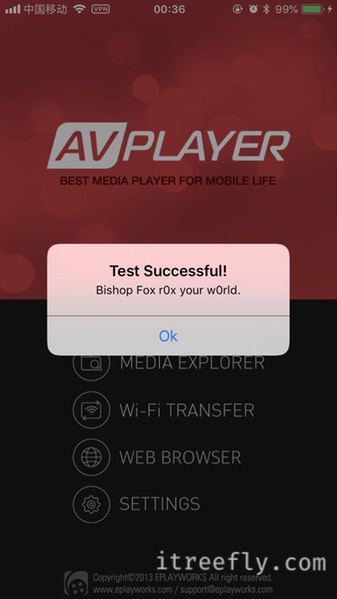
测试注入功能
[Bash shell] 纯文本查看 复制代码 tree-flys-iPhone-7:~/bfinject root# bash bfinject -P AVPlayer.app -L test
[+] Electra detected.
*** RAND = 1c9cf2572f0064d69005b0e4bd2ae5a2
*** RANDOM_NAME = /bootstrap/usr/local/bin/91432177bcba40fb1d026bcf83203e13
[+] Injecting into '/var/containers/Bundle/Application/B36F534E-DF04-4BBF-987B-EED3E4B3A6AC/AVPlayer.app/AVPlayer'
[+] Getting Team ID from target application...
[+] Thinning dylib into non-fat arm64 image
[+] Signing injectable .dylib with Team ID DR9UPY28XM and platform entitlements...
[bfinject4realz] Calling task_for_pid() for PID 2627.
[bfinject4realz] Calling thread_create() on PID 2627
[bfinject4realz] Looking for ROP gadget... found at 0x1849b7118
[bfinject4realz] Fake stack frame at 0x108998000
[bfinject4realz] Calling _pthread_set_self() at 0x184c8471c...
[bfinject4realz] Returned from '_pthread_set_self'
[bfinject4realz] Calling dlopen() at 0x1849b6e7c...
[bfinject4realz] Returned from 'dlopen'
[bfinject4realz] Success! Library was loaded at 0x1c0167bc0
[+] So long and thanks for all the fish. | 





 IP卡
IP卡
 发表于 2018-7-19 01:43:16
发表于 2018-7-19 01:43:16
 提升卡
提升卡 置顶卡
置顶卡 变色卡
变色卡 千斤顶
千斤顶 显身卡
显身卡
 发表于 2018-7-19 06:49:18
发表于 2018-7-19 06:49:18

 发表于 2018-7-19 09:37:12
发表于 2018-7-19 09:37:12

 发表于 2018-7-19 09:51:43
发表于 2018-7-19 09:51:43
 发表于 2018-7-19 14:27:28
发表于 2018-7-19 14:27:28
 发表于 2018-7-19 23:26:54
发表于 2018-7-19 23:26:54

 楼主
楼主